Routing security – getting better, but no reason to rest!
In January last year I looked back at 2017 trying to figure out how routing security looked like globally and on a country level. I used BGPStream.com – a great public service providing information about suspicious events in the routing system.
The metrics I used for this analysis were number of incidents and networks involved, either by causing such incidents, or being affected by them.
An ‘incident’ is a suspicious change in the state of the routing system that can be attributed to an outage or a routing attack, like a route leak or hijack (either intentional or due to a configuration mistake). BGPStream is an operational tool that tries to minimize false positives, so the number of incidents may be on the low side.
Of course, there are a few caveats with this analysis – since any route view is incomplete and the intents of the changes are unknown, there are false positives. Some of the incidents went under the radar. Finally, the country attribution is based on geo-mapping and sometimes gets it wrong.
However, even if there are inaccuracies in details, applying the same methodology for a new dataset – 2018 – gives us a pretty accurate picture of the evolution.
Here are the highlights of some changes in routing security in 2018, compared to 2017.
- 12,600 ( a 9.6% decrease) total incidents (either outages or attacks, like route leaks and hijacks).
- Although the overall number of incidents was reduced, the ratio of outages vs routing security incidents remained unchanged – 62/38.
- About 4.4% (a decrease of 1%) of all Autonomous Systems on the Internet were affected.
- 2,737 (a decrease of 12%) Autonomous Systems were a victim of at least one routing incident.
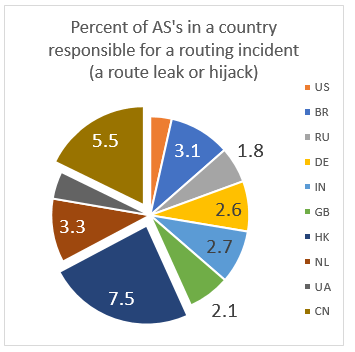
- 1,294 (a 17% decrease!) networks were responsible for 4739 routing incidents (a 10.6% decrease).
The bottom line – we did much better last year than the year before. Is it accidental, or part of a positive trend? This is hard to say yet, although in my experience there is much more awareness, attention and discussions of the challenges of routing security and helpful solutions recently.
Let us look in more details at what was happening in the global routing system in 2018.
Starting with “victims” – networks that were potentially affected by a routing security incident, a hijack or a routing leak. Potentially – because I do not try to analyze the impact, just taking into account the fact that, for instance, a prefix belonging to a victim network was hijacked by another network – a culprit. To what extent the victim was affected is a very interesting question, but beyond the scope of this article.
In absolute numbers, the US are leading the top-10 list with 623 networks being affected by 1244 routing incidents. They are followed by Brazil (231 victims), Russia (171) and Bangladesh (151). However, if we normalize these data by the number of advertised AS’s in a country, the distribution looks differently:
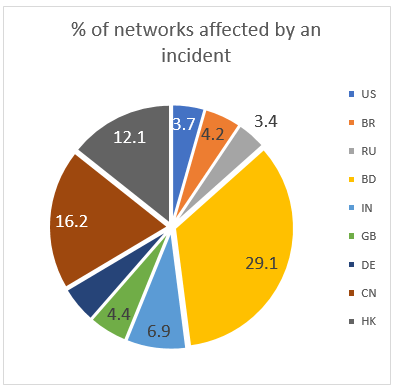
Bangladesh, China and Hong-Kong appear to be the most vulnerable with up to 30% of all networks affected by a routing mishap.
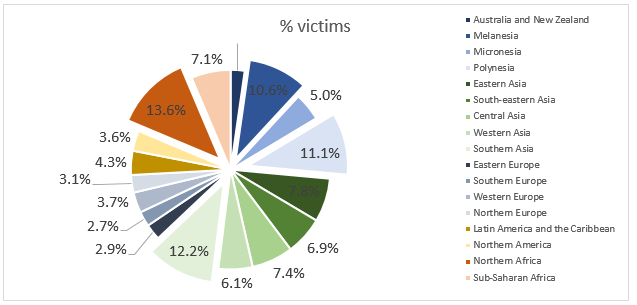
If we zoom out and look at the statistics at the regional level, Northern Africa, Southern Asia, Polynesia and Melanesia will be at the top.
Moving on to networks whose configuration mistakes or intentional acts caused these incidents. Although Micronesia leads the list, only one network of 20 that operate in the region was implicated in an incident. The situation is worse in Sub-Saharan Africa where 50 networks out of 1106 caused a leak or a hijack. They are followed by Eastern Asia, Southern Asia and Latin America and the Caribbean with at least 3.3% of all networks not exercising proper routing hygiene.
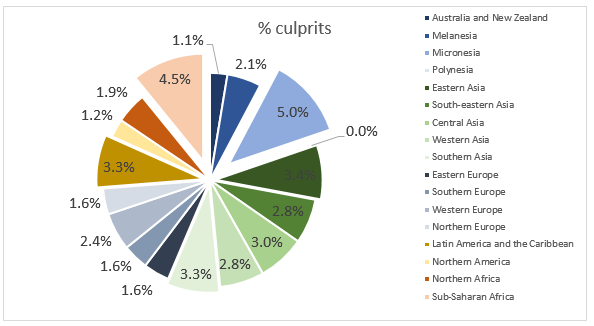
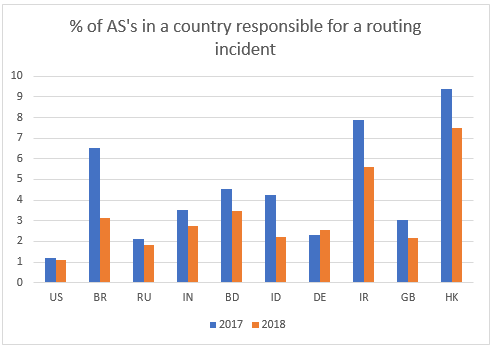
On the country level 36% of all culprits operate in the US, Brazil and Russia, but if we normalize this by the total number of networks in a country, mainland China and Hong-Kong will be at the top. The latter got in the list because of Telstra International (AS4637), implicated in several suspicious announcements looking like route leaks.
Finally, looking at the dynamics, the situation has improved, compared to 2017 – almost in every country in the top-10 list the percentage of culprits reduced, most visibly in Brazil and Indonesia.
Although comparing just two years cannot say a lot about a long-term trend, overall, I feel we are moving in the right direction. More awareness and attention to the issues of routing security in the network operator community, rejuvenated interest to RPKI and some positive trends I provided here support this.
I’d like to believe that efforts like MANRS also contributed to this positive trend. MANRS, an industry-driven initiative supported by the Internet Society, provides an opportunity to strengthen the community of security-minded operators and instigate a cultural change. MANRS defines a minimum routing security baseline that networks are required to implement to join. The more service providers join MANRS, the more gravity the security baseline gets, the more unacceptable will be lack of these controls, the fewer incidents there will be, and the less damage they can do.
This baseline is defined through four MANRS Actions:
- Filtering – Ensure the correctness of your own announcements and of announcements from your customers to adjacent networks with prefix and AS-path granularity
- Anti-spoofing – Enable source address validation for at least single-homed stub customer networks, your own end-users, and infrastructure
- Coordination – Maintain globally accessible up-to-date contact information
- Global Validation – Publish your data, so others can validate routing information on a global scale.
Maintaining up-to-date filters for customer announcements could mitigate many route leaks. Preventing address squatting could help ward off things like spam and malware. Keeping complete and accurate routing policy data in Internet Routing Registry (IRR) or Resource Public Key Infrastructure (RPKI) repositories are essential for global validation that helps prevent BGP prefix hijacking. Having updated contact information is vital to solving network emergencies quickly.
Last year the community also developed MANRS for IXPs. Another baseline, allowing an IXP to build “safe neighborhood” with the participating networks. Most important, and therefore mandatory for joining, Actions are:
- Prevent propagation of incorrect routing information. Requires IXPs to implement filtering of route announcements at the Route Server based on routing information data (IRR and/or RPKI).
- Promote MANRS to the IXP membership. IXPs joining MANRS are expected to provide encouragement or assistance for their members to implement MANRS actions.
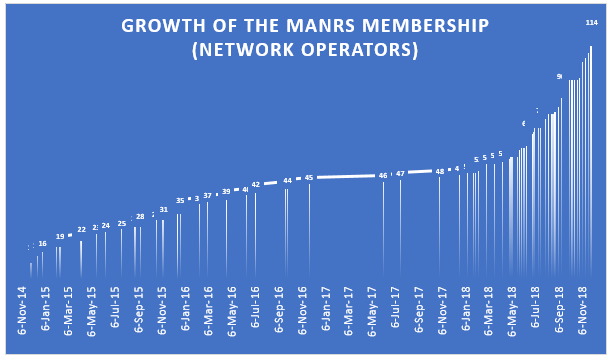
In 2018 we saw a significant uptake in MANRS, too. In one year the number of participants more than doubled, reaching 120, and the MANRS IXP Programme grew up to 28 IXPs in a year.
Let us hope all the positive trends continue in 2019. And it is not hope alone – every network can influence this future. Because once connected to the Internet – we are part of the Internet.
Leave a Comment